Qualys, Inc. announced Container Runtime Security, which provides runtime defense capabilities for containerized applications.
This revolutionary new approach instruments an extremely lightweight snippet of Qualys code into the container image, enabling policy-driven monitoring, detection and blocking of container behavior at runtime. This capability eliminates the need for cumbersome management of sidecar and privileged containers by security solutions that are difficult to manage and administer on host nodes and don’t work in container-as-a-service environments. Qualys Runtime Container Security, once instrumented in the image, will work within each container irrespective of where the container is instantiated and does not need any additional administration containers. This new solution addresses, in real time, container security use cases like critical file-access monitoring and blocking, network micro-segmentation, vulnerability and exploit mitigation, and virtual patching.
“At Zoom, we continue to enhance our comprehensive security program that addresses prevention, detection and response capabilities across all types of workloads,” said Randolph Barr, Head of Security Operations at Zoom. “Enforcing security best practices, mitigating attacks and monitoring are key use cases for container runtime security. Qualys Container Runtime Security will be key to further extending our detection and response capabilities to containerized workloads running on any container infrastructure.”
Now security teams can implement a comprehensive container security program with a single solution that includes vulnerability management, and detection and response across the build-ship-run container pipeline. With Qualys Container Runtime Security, customers can:
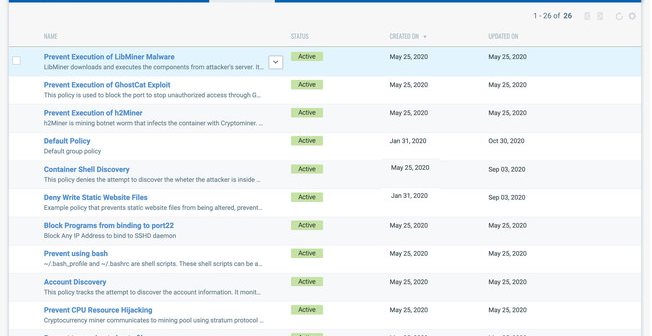
- Perform comprehensive, policy-driven monitoring and blocking of container runtime behavior including file access, network communications and process behaviors
- Create granular custom behavioral policies, use policies from the built-in policy library or automatically generate policies based on learned container behaviors
- Instrument container images in the CI/CD build pipeline with an innovative “follow the image” instrumentation approach which allows for standardized, guaranteed container runtime security across all types of container environments like Docker, Kubernetes, AWS Elastic Kubernetes Service, AWS Elastic Container Service, Azure Kubernetes Service, and Google Kubernetes Engine, as well as including container-as-a-service environments like Azure Container Instances, AWS Fargate and Google CloudRun.
“The growth of Kubernetes comes at a time when it is adept at solving many pertinent problems in IT and software development today. However, new tools are needed to secure containers, as container-based application development is a completely different approach to software,” said Frank Dickson, program vice president, Security Products at IDC. “Kubernetes can be managed as immutable infrastructure; however, the reality is that container configurations can drift during runtime. The Qualys approach empowers security to follow the container image with built-in instrumentation, enabling visibility and behavior enforcement for running containers. The solution also facilitates a ‘follow the container’ approach, providing DevOps and application teams future-proof development protection as applications migrate to more mature container and managed container environments such as Docker, Kubernetes, AWS Fargate and others.”
“Detection and Response in a single application across the container DevOps pipeline is key to effectively secure the containerized applications, as the high-velocity DevOps container pipeline can be exploited by malicious actors at runtime,” said Philippe Courtot, chairman and CEO of Qualys. “Therefore, we must build security into cloud workloads and extend protection into running containers. Qualys brings defense capabilities to our Container Security solution with the addition of policy-driven behavior detection and response capabilities to protect running containers on-premises, in private clouds or in container-as-a-service public clouds.”