With each passing year, password day seems to become less and less relevant. In 2024, the average person had 170 personal passwords and 87 business- related passwords. This number has dropped to 120 personal and 67 work-related passwords in 2026. While the number of passwords per person is decreasing, we still haven’t reached the ideal of passwordless entry.
Passwords are still part of our daily lives, and we need to protect them while they still exist. To highlight the importance of protecting entry, we have gathered commentary from experts in the security industry. We hope you find value in their advice.
Reduce Password-dependent Systems
Password Day should be less about making passwords stronger and more about reducing how many systems depend on them. The real shift is toward traceable identity, consent, and access across systems.
Ken Herron, Co-Founder, VCONify
Focus on Password Length
Most password guidance is well intentioned but still shaped by outdated rules that don’t account for human behavior. When people are forced into strict complexity requirements, they naturally take shortcuts like predictable patterns and small variations that are easy to guess. In reality, password strength is driven primarily by length, not complexity.
Zach Varnell, Founder, Asteros
The World is Moving to Biometric Assured Identity
Password Security Needs to Go Beyond IT Department Password Management
The use of passwords for security purposes is no longer simply an issue of how well your IT department manages those passwords, it has become a risk to your business. Using passwords alone in today’s world will not be sufficient; we must begin using multi-factor authentication and move toward passwordless systems. While this shift is largely based on new technologies and products available today, the largest part of this shift will come from changing user behavior and increasing user awareness.
Richard Govada Joshua, IT Project Manager, TEKsystems
Steer Clear of Shame-based Security
Shame-based security doesn’t work, it just teaches people to hide their workarounds. Most users aren’t ignoring password best practices because they don’t care, they’re ignoring them because remembering 200 unique logins isn’t a reasonable ask, and we’ve spent two decades pretending it is. The leaders who’ll actually move the needle are the ones replacing the lecture with real tools (password managers, passkeys, MFA) and explaining the why in language that doesn’t make people feel dumb for asking.
Lakeidra Smith, Founder, The Cyber Consultant
Password Security Breaks Down in Day-to-day Use
At Zibtek, we’ve learned that password security usually breaks down in day-to-day use, not in the policy itself. Teams don’t follow complicated rules consistently, especially when they slow things down. The better approach is keeping things simple use multi-factor authentication, limit access where possible, and make secure habits easy to maintain. When that’s in place, you don’t have to rely on perfect password behavior.
Cache Merrill, Founder, Zibtek
Mindsets Need to Shift to Zero Standing Privilege
World Password Day feels increasingly outdated. Passwords can no longer be relied on as a meaningful line of defense as they are routinely bypassed through social engineering, and we are seeing increased attacks through third-party apps. Organizations can build true resilience by rethinking access altogether and adopting ephemeral permissions and just-in-time (JIT) access to ensure privileges exist only when needed and drastically reduce the window of opportunity for attackers.
Ultimately, organizations’ mindsets must shift toward a model of zero standing privilege where no user, device, or agent is inherently trusted, and every access request is continuously verified.
Pierre Mouallem, CISO, Delinea
Password Protection is Also About Protecting Machines
World Password Day is no longer just about protecting people. It’s now also about protecting machines. As machine-to-machine communication accelerates, strong, frequently rotated credentials are essential to ensure trusted systems don’t execute malicious or compromised instructions.
The challenge, however, is that many organizations still rely on static credentials. Long-lived API keys and persistent service account passwords create machine credentials with unlimited replay value. When credentials become permanent, compromise becomes persistent. If these credentials leak through logs, configuration files, AI, or repositories, attackers can impersonate trusted systems for extended periods without triggering the authentication signals typically associated with human access.
Modern security requires a shift to short-lived, cryptographic identities, where every workload proves what it is through mechanisms like mutual TLS authentication and temporary identity tokens. This ensures every interaction is verifiable and resilient by design.
The future of cybersecurity will be defined by how effectively we secure the machines that now act on our behalf, and passwords continue to play an important role in the evolving security journey.
Kevin Higgins, Senior Consultant, Optiv
Passwords Are Only One of Many Credentials Under Attack
World Password Day 2026 brings the usual advice for passwords: longer, unique, never reused. That is no longer enough. Passwords are only one of many credentials now under AI-powered attack. Generative AI has industrialized credential attacks: phishing lures that defeat traditional user training, voice clones that pass help-desk identity checks, and credential stuffing at industrial scale.
Credentials remain one of the top initial access vectors year-after-year, and non-human identities, from AI agents to service accounts, are multiplying, each one holding credentials, each one a potential blast radius. When the next breach arrives, “we didn’t know who or what had access” will not be acceptable as a defense.
The fix is not novel. For organizations: phishing-resistant multi-factor authentication (MFA) and passkeys, single sign-on wired into a disciplined joiner-mover-leaver process, vaulted privileged access, and scoped, logged, revocable credentials for every non-human identity, AI agents included, never a shared service account. For individuals: a password manager, unique passwords or passkeys, and MFA on every account. The password era is ending, the credential era is not. Most breaches still begin with a credential someone forgot to protect, revoke, rotate, or retire. The organizations and individuals that master that unglamorous work are the ones that stay resilient when the next AI-powered attack lands.
Jack Cherkas, Global CISO, Syntax
Security Behind the Scenes
The industry is moving toward a future where passwords fade into the background – or disappear entirely – replaced by stronger, smarter authentication methods built on cryptography, trusted devices, and identity-bound access. When security depends on people remembering complex secrets, failure is almost guaranteed. When security is designed to happen behind the scenes, organizations can reduce phishing and credential theft, eliminate password reuse, and strengthen protection without adding friction. The goal shouldn’t be better passwords or password managers. It should be a world that no longer asks people to manage passwords at all.
Steve Shoaff, SVP of Transformation, Imprivata
Verification Strategies Must Evolve
Compromised credentials remain the most common attack vector in data breaches, yet according to recent research, 74% of U.S. banking customers continue to rely on passwords as their primary login method. As fraudsters increasingly target authentication flows and account takeover attacks surge, verification strategies must evolve. Security cannot be compromised for convenience when money, accounts, and personal data are on the line. The key is to use authentication methods that consumers already trust, like biometrics, to reduce resistance, support adoption, and help create secure experiences that feel familiar rather than disruptive.
Rishi Kaushal, CIO, Entrust
Identity is the Real Control Point
Passwords used to be the backbone of security, but they are starting to show their age. They were not built for a world where identities include not just people, but also apps, services, and now AI agents acting on their own. That shift makes identity the real control point. It is no longer enough to protect a login. You need to know who or what is accessing your environment, what they are allowed to do, and whether that behavior actually makes sense. Passwords can still play a role, but only as part of a bigger picture. Strong authentication, least privilege access, and continuous monitoring are what actually keep things in check. As AI becomes more embedded in day-to-day operations, the focus has to move from just securing credentials to managing and understanding every identity in the system.
Tim Chase, Field CISO & Principal Technical Evangelist, Orca Security
Rethink How Identities are Secured
As AI continues to evolve and cyberattacks become increasingly sophisticated, much of our digital security still hinges on a single weak point: the password. It’s telling that 39% of people say AI-powered phishing is the threat they fear most, yet less than a quarter feel highly confident in spotting what’s real versus a scam. This gap highlights a growing vulnerability and a critical opportunity to rethink how we secure identities.
Authentication must evolve to meet today’s threat landscape. Passwordless solutions are rapidly replacing traditional passwords with stronger, more user-centric methods like biometrics, authenticator apps, and digital certificates. These approaches significantly reduce the risk of phishing and credential theft while improving the user experience.
World Password Day shouldn’t just be about updating passwords. It should spark a broader shift. To stay ahead of modern threats, organizations and individuals need to move beyond passwords and adopt more resilient authentication strategies that put control back in the hands of users.
John Cannava, CIO, Ping Identity
Ensure the Right Users Have the Right Access at the Right Time
World Password Day is a good reminder that passwords alone are no longer enough to protect modern organizations. As AI makes it easier for attackers to scale credential-based attacks, the real challenge is ensuring the right users have the right access at the right time. That means organizations need better visibility into who has access to what, and stronger controls to manage and adjust that access as risks change. Ultimately, reducing reliance on passwords starts with taking a more proactive approach to managing identity and access across the business.
Control Passwords While They Still Exist
We’re living in the middle. Passkeys are growing, passwords are lingering, and identity has become the control plane for everything. That tension is where risk lives.
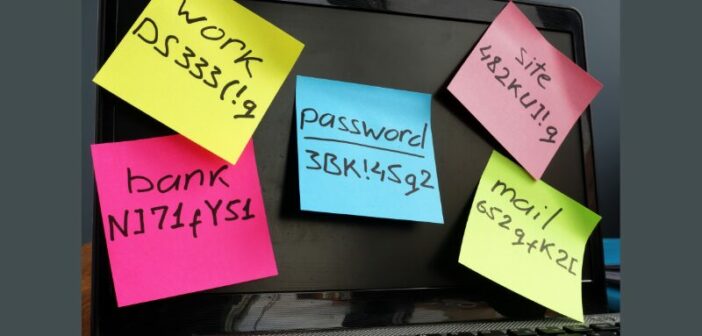
And then there’s the human side. We forget. We reuse. We share when it’s easier than doing it right. At 20 people, you can get away with it. At 100, it starts to crack. At scale, it breaks quietly—no big event, just small gaps that add up.
So what do you do—not in some future state, but right now, while passwords still exist?
You don’t chase perfection. You control what’s real. Who has access, where it lives, how it’s used, and when it changes.
Grady Summers, CEO, Netwrix
Guessable Passwords Are Still Mainstream, But They Shouldn’t Be
The most commonly used password remains exactly what you think it is: ‘123456,’ according to NordPass’s latest annual report on passwords exposed in global data breaches. My first instinct was to dismiss this — surely this couldn’t still be true — but after testing it myself, the unfortunate answer is YES: guessable passwords like ‘1234567’ still work on mainstream sites such as Evite, Facebook, and X, though some offer advice on stronger passwords. While the finance industry has been forced to modernize authentication, similar legislation should extend to all industries regardless of the service being accessed. It’s time to ditch outdated passwords and move to more appropriate security for today’s internet.
Tony Anscombe, Chief Security Evangelist, ESET
Treat Security Like a Continuously Managed System
Stop Habits Criminals Are Looking For
Password Day shouldn’t be about telling people to add another symbol to the end of a password, it should be about stopping the habits criminals already know to look for. Longer, memorable passwords are usually better than short, complicated ones people keep reusing, especially when they’re supported by multi-factor authentication.
SIM Cards as A Credential
Carlos DaSilva, CPO, Unibeam
A Truly Secure Future is One Without Passwords
I don’t believe in World Password Day because I think passwords are the real problem in cybersecurity. It’s amazing to me that decades after the rise of the internet, we’re still relying on a system that shifts risk onto users and then blames them when it fails. Any organisation that still depends solely on passwords isn’t secure; it’s just been lucky so far. A truly secure future is one without passwords. Anything less is a compliance and risk management failure waiting to happen.
Naomi Grossman, compliance manager, VinciWorks
Password Reuse Creates Unnecessary Risk
World Password Day reminds us that password reuse still creates unnecessary risk. Bitwarden research found that 79% of Gen Z admit password reuse is risky, yet 59% recycle an existing password when updating accounts after a company discloses a data breach. Strong, unique passwords stored in a password manager remain essential because a single reused password can turn one compromised account into many. Users should turn on two-factor authentication (2FA) whenever possible to add another security layer for high-value accounts like primary email and bank logins. Passkeys can also provide stronger phishing-resistant authentication where supported.
Gary Orenstein, Chief Customer Officer, Bitwarden
Passkeys Are a Step Not the Destination
The industry is converging on Passkeys as the answer to passwords, and there’s even a movement to rename May 7 “World Passkeys Day”, but Passkeys are a step, not the destination.
What users and businesses should be demanding is No User Action for online access: letting the endpoint device itself perform continuous, cryptographic verification in the background, with no codes, no prompts, and no taps once the user has logged into their device.
Public-key cryptography combined with the trusted hardware already in every modern laptop and phone makes this not only possible but practical today, and it’s the only path that delivers on Zero Trust’s promise of “always verify” without putting the burden and the risk back on the user. The technology exists; what’s missing is the demand.
Thi Nguyen-Huu, founder and CEO, WinMagic
More Security News
Related News: