Identity has become the most targeted attack surface in modern cybersecurity. Compromised credentials, lateral movement, and privilege escalation now drive most breaches, yet traditional tools were not built to detect identity-centric attacks. This evolution has made Identity Threat Detection and Response (ITDR) one of the most important categories in security.
Below is a detailed look at the top seven ITDR vendors, according to Gartner’s peer insights, ranked by the number of ratings each vendor has. Read on to discover what they do well, where they fall short and which organizations benefit most from their platforms.
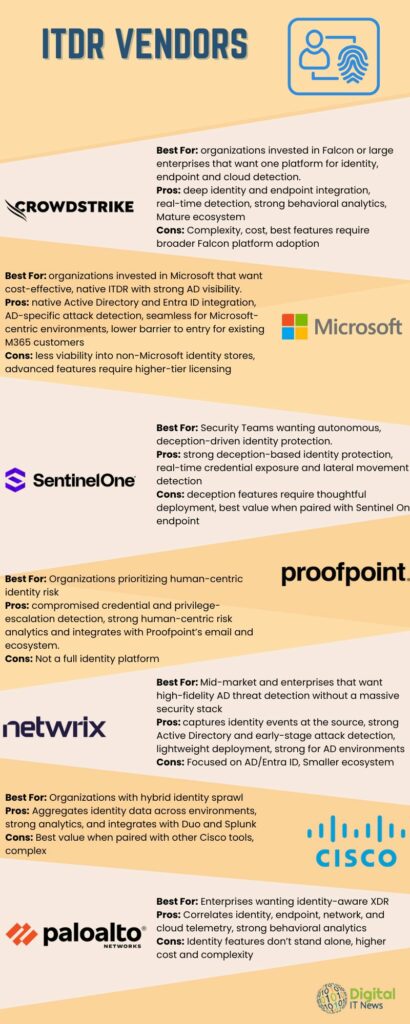
1. CrowdStrike: Falcon Next‑Gen Identity Security
CrowdStrike’s Falcon Next‑Gen Identity Security platform brings together identity and endpoint protection, providing organizations with real‑time visibility into identity‑based attacks. By unifying telemetry across users, devices and authentication flows, it helps security teams detect credential misuse, lateral movement and privilege escalation before attackers gain meaningful footholds. The platform’s strength lies in its ability to correlate identity behavior with endpoint activity, allowing rapid detection and automated responses that reduce dwell time and operational overhead.
CrowdStrike’s approach is particularly effective for organizations that already rely on the Falcon ecosystem, as the identity module integrates seamlessly with the broader platform. While the solution is powerful, it can be resource‑intensive for smaller teams and its most advanced capabilities are unlocked only when paired with additional Falcon components. Still, for enterprises seeking a unified, AI‑driven identity and endpoint defense strategy, CrowdStrike remains one of the strongest ITDR options available.
2. Microsoft: Defender for Identity
Microsoft Defender for Identity focuses on detecting and investigating identity‑related threats within on‑premises Active Directory environments. It continuously monitors user behavior, permissions and authentication patterns to identify suspicious activity, such as credential theft, privilege escalation and lateral movement. Because of its deep integration with Active Directory and Entra ID, it provides visibility into attack paths often hidden by traditional security tools.
Organizations already invested in Microsoft 365 benefit from a streamlined deployment experience and native integration across the Microsoft security stack. However, the platform delivers its strongest results in Microsoft-centric environments and provides limited visibility into non-Microsoft identity stores. For companies with hybrid or legacy AD infrastructure, Defender for Identity offers a cost‑effective and tightly integrated ITDR solution that enhances existing Microsoft security investments.
3. SentinelOne: Singularity Identity
SentinelOne’s Singularity Identity platform is built to detect and protect against identity‑based threats through real‑time monitoring of credential exposure, lateral movement attempts and impersonation activity. It uses deception‑based techniques to mislead attackers, feeding them false identity artifacts and redirecting malicious activity into controlled environments. This approach allows security teams to detect threats earlier in the attack chain and respond with precision.
The platform integrates closely with SentinelOne’s autonomous EDR/XDR capabilities, creating a unified detection and response ecosystem. While the deception‑driven model is powerful, it requires thoughtful planning to deploy effectively, and organizations see the greatest value when they are already using SentinelOne for endpoint security. For teams seeking an automated, deception‑enhanced identity defense strategy, Singularity Identity offers a differentiated and highly effective ITDR solution.
4. Proofpoint: Identity Threat Defense
Proofpoint Identity Threat Defense focuses on detecting compromised credentials, privilege escalation and lateral movement by analyzing identity‑related activity across enterprise environments. Its strength lies in its ability to identify human‑centric risks, particularly those stemming from phishing, social engineering and insider threats. By correlating identity behavior with Proofpoint’s broader threat intelligence, the platform provides a more complete picture of how attackers target users.
Because Proofpoint’s ecosystem centers around email and human‑risk analytics, its ITDR capabilities complement its existing strengths rather than functioning as a standalone identity platform. Organizations that already rely on Proofpoint for email security or insider‑threat monitoring will find the integration especially valuable. For companies prioritizing the detection of identity compromise driven by user‑focused attacks, Proofpoint delivers strong visibility and actionable insights.
5. Netwrix: Threat Prevention (ITDR)
Netwrix Threat Prevention protects Active Directory by capturing identity events directly at the source rather than relying solely on native logs. This approach provides earlier detection of credential misuse, suspicious authentication activity and privilege escalation attempts. By focusing on AD and Entra ID, the identity backbone of most enterprises, Netwrix delivers high‑fidelity visibility into the earliest stages of identity‑based attacks.
The platform is lightweight, fast to deploy and well‑suited for organizations that want strong AD threat detection without adopting a large, complex security suite. While its focus is narrower than some competitors, its precision and simplicity make it a strong fit for mid‑market and enterprise environments with hybrid identity infrastructure. For teams seeking reliable, low‑overhead ITDR capabilities centered on Active Directory, Netwrix offers a practical and effective solution.
6. Cisco: Identity Intelligence
Cisco Identity Intelligence aggregates identity data across hybrid and multi‑cloud environments, giving organizations a unified view of identity posture and risk. By combining analytics and artificial intelligence, it identifies anomalies in authentication patterns, access behavior and identity relationships that may indicate compromise. Its ability to ingest identity data from multiple sources makes it particularly valuable for organizations with complex or distributed identity architectures.
The platform integrates with Cisco’s broader security ecosystem, including Duo and Splunk, enabling deeper correlation across authentication, network and application activity. While this creates a powerful identity‑centric detection framework, it can also introduce complexity for smaller teams or organizations not already invested in Cisco technologies. For enterprises with hybrid identity sprawl, Cisco Identity Intelligence provides a strong foundation for identity‑aware threat detection and response.
7. Palo Alto Networks: Cortex XDR (Identity Capabilities)
Palo Alto Networks’ Cortex XDR brings identity into its extended detection and response platform by correlating identity, endpoint, network and cloud telemetry. This cross‑domain visibility allows security teams to detect suspicious identity behavior in the context of broader attack activity. By analyzing authentication patterns, access anomalies and privilege usage, Cortex XDR helps identify identity‑driven threats that might otherwise go unnoticed.
Because identity capabilities are embedded within the larger XDR platform, organizations benefit from a unified detection and response workflow. However, this also means that identity features are not available as a standalone product, and the platform’s cost and complexity may exceed the needs of smaller organizations. For enterprises seeking identity‑aware XDR with strong automation and deep correlation across security domains, Cortex XDR is a compelling option.
Which Is Best For You?
Identity is now the core of modern cybersecurity, and the vendors leading the ITDR space reflect that shift. CrowdStrike, Cisco and Palo Alto Networks excel in large, complex environments that require broad cross‑domain visibility. Microsoft and Netwrix offer strong, cost‑efficient protection for AD‑centric organizations. Proofpoint and SentinelOne shine in human‑centric and deception‑driven use cases. Which one is the best fit for you depends on your needs.
More Security News
Related News:
Top 10 File and Object Storage Platforms
Comparing Today’s Leading DEX Platforms
A PC Alternative Endpoint Showdown in a Memory-Constrained World

